About the Author
Jeremy Van der Haegen is a Belgian freelance journalist who covers business and politics of the Asia-Pacific, cryptocurrencies, and blockchain technology.
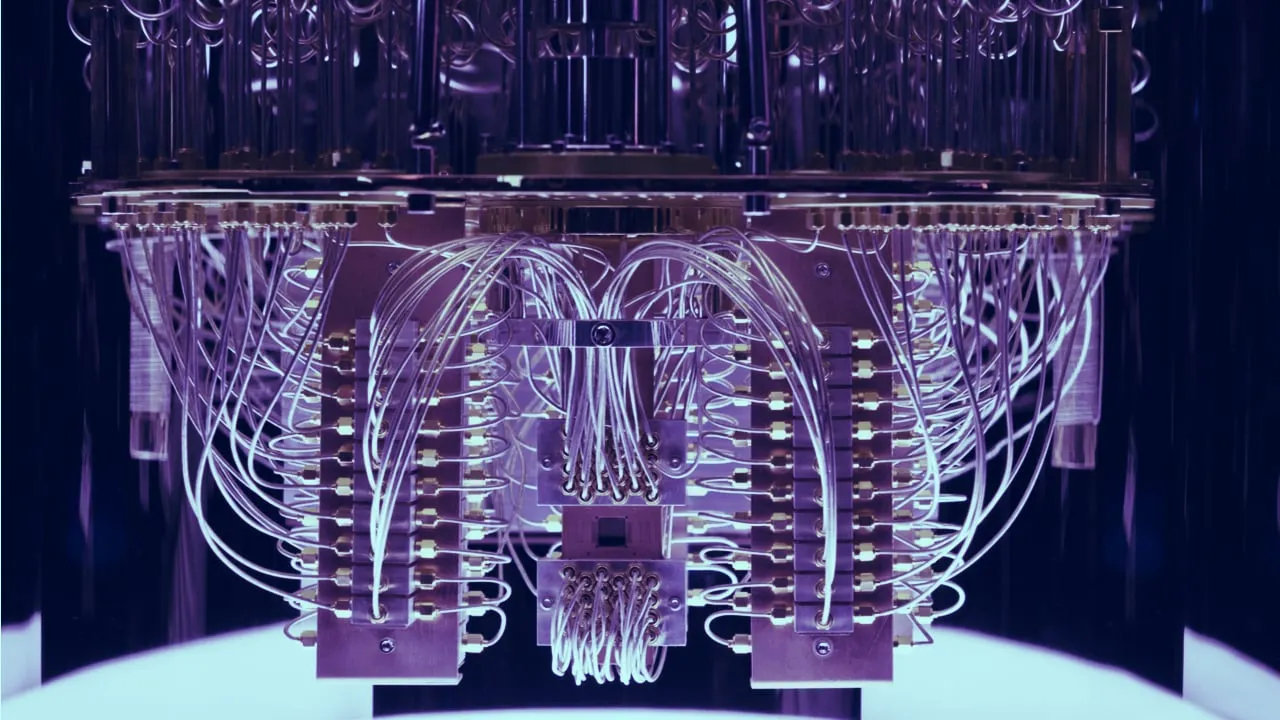
One of the most overlooked problems of blockchain systems is their ability to resist the fast-evolving machines known as quantum computers.
These powerful computers use quantum physics to solve complex problems that are beyond the reach of traditional devices by using qubits—an evolution of the classic binary bit. Qubits are able to represent the value 1 or 0 at the same time, which promises to deliver an exponential increase of computing power.
The world’s top superpowers are pouring billions of dollars into the development of this technology—and for good reason. The first nation or company to harness quantum computing will be poised to crack the encryption protecting rivals' sensitive documents.
In the case of blockchain systems, the cryptography protecting their tamper-proof ledgers may be at risk. Researchers at the University of Sussex estimated in February that a quantum computer with 1.9 billion qubits could essentially crack the encryption safeguarding Bitcoin within a mere 10 minutes. Just 13 million qubits could do the job in about a day.
Fortunately, the ability to deploy quantum computers with so many qubits still seems many years away. IBM unveiled its 127-qubit processor just last year, while a unit sporting 1,000 qubits is set to be completed by the end of 2023.
“We’re not there yet,” said Jens Groth, a Danish professor in cryptology and encryption researcher at Dfinity. “Nobody knows what the exact time frame looks like, but blockchain might only be at risk within 10 to 20 years.”
Groth underlines that there’s an important distinction between two types of qubits—physical and logical ones. The latter describes a qubit that achieves a superposition between 1 and 0 via a quantum gate. A logical qubit consists of nine physical qubits. “Company announcements about a novel qubit milestone usually concern physical qubits, not logical ones,” he explains.
Defenders have the upper hand
Although researchers like Groth don’t classify quantum computers as an immediate threat to blockchain technology, experimentation with solutions is nevertheless ongoing. “Cryptographers do reflect on what a suitable countermeasure would look like,” Groth says.
Blockchain developers have a clear advantage in the race to defend against mounting computing power. Specifically, they can increase the number of digits in the cryptographic keys that protect the chain—a process that’s faster to scale than it is for the attackers to catch up. “The defenders are winning this battle in the long run,” Groth claims.
This is evident in the field of symmetric key encryption when examining the popular Advanced Encryption Standard (AES). The most common variation of 128 keys could be cracked by quantum computers and even classic attackers. However the AES 256 variation, featuring twice the amount of keys, appears strong enough to fend off brute force attacks by quantum machines for the foreseeable future.
Some cryptographers, however, are cautious about deeming encryption the automatic winner in a post-quantum world. “It’s very hard to predict whether we will manage to continually scale up key sizes against powerful quantum computers,” says Angshuman Karmakar, a research associate at the Computer Security and Industrial Cryptography group (COSIC) of the KU Leuven.
“You always have to take a pessimistic approach when you’re on the defending side. A new brilliant algorithm could pop up and suddenly put attackers at an advantage. The probability of this happening is extremely low, but can never be ruled out,” Karmakar says.
Meanwhile, lattice-based cryptography offers another potential solution to quantum attacks. This type of encryption adds mathematical noise that could even confuse a futuristic supercomputer. “Quantum computers could find a needle in a haystack by constantly doubling the probability of finding it. You need to design structures that these computers can’t take advantage of,” Groth says.
According to Karmakar, lattice-based solutions are currently in the process of standardizing and should be ready for public use soon. “A lot will depend on how fast the industry can apply new encryption. On the other hand, there’s a lot of time left before quantum computers reach a level where they could crack a blockchain,” he says.
Switching to a new private key
Implementing an encryption upgrade for a blockchain system seems to be the biggest headache for cryptographers. In a typical blockchain like Bitcoin, every node will have to be convinced to switch to a new encryption method. Governance protocols like the Internet Computer could automatically update their system through user voting. Collective determination will be essential in all cases.
The process of upgrading existing private keys, however, could create new vulnerabilities. That’s because, according to Groth, new keys will be generated by the system after successfully implementing post-quantum encryption. To activate a switch to the new key, users will have to sign for approval with their old one.
However, inactive users might never upgrade their private key, which could cause serious problems. Sizable dormant wallets, like the ones containing around 1 million Bitcoins that supposedly belong to Satoshi Nakamoto, likely will never see an encryption enhancement. This could leave certain legacy portions of the crypto ecosystem open to quantum-based attacks even if the blockchain they rely on has been safely upgraded.
The bottom line is, while blockchains appear safe for now from quantum computing, developers will need to stay vigilant and be ready to take new steps to ensure this remains true.