In brief
- One Reddit user lost $1,200 in Ethereum after he accidentally left his seed phrase in a GitHub upload.
- The data was immediately scanned by malicious bots that monitor code commits.
- It took hackers less than two minutes to siphon the funds.
A Reddit user has lost $1,200 worth of Ethereum after he accidentally left his wallet’s recovery phrase in a GitHub repository, an online file storage area. While this is—or at the very least should be—an uncommon situation, it turned out that hackers had already prepared malicious bots, since the user’s funds disappeared in less than two minutes.
“A hacker got my mnemonic and stole $1,200 in ethereum from my Metamask wallet in under 100 seconds. The hackers were using a bot to scan for the mnemonic phrases across GitHub, and I accidentally left it in my code on a GitHub repo while I was sending to a Hack Money hack-at-hon,” the Redditor wrote today.
Mnemonic (or seed) phrases are combinations of 12 words set in a specific order, which allow you to restore access to a crypto wallet. Essentially, they are “the last line of defense” alongside private keys (the password that lets you spend coins). If someone gets ahold of one, they can get full access to your wallet and funds that are being kept in it.
In short, you shouldn’t upload your private keys or seed phrase on public, open-source repositories such as GitHub—or anywhere else that's public for that matter.
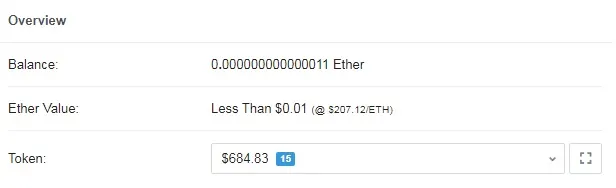
The user noted that he still has almost $700 worth of ERC-20 tokens locked in the Compound DeFi protocol (cETH), which is used for lending crypto to other people. But if he withdraws the money, it gets sent to the wallet where the bot is siphoning out every bit of ETH. He can't win.
In Ethereum, you need a token to pay transaction fees (called “gas”) to transfer your tokens. If two people try to move the same amount of Ethereum at the same time, it’s likely that the one with the greater fees will get processed. But the bot is automatically submitting transactions with higher fees—winning the race every time.
“Although there are some coins and tokens left, the bot will siphon any ethereum I have to prevent me from moving my coins, and/or outmatch my attempts by supplying more gas,” the user explained.
A feline standoff
A somewhat similar case was reported last September when hackers compromised a wallet that contained a number of rare CryptoKitties—non-fungible Ethereum tokens, each representing a unique digital “cat.”
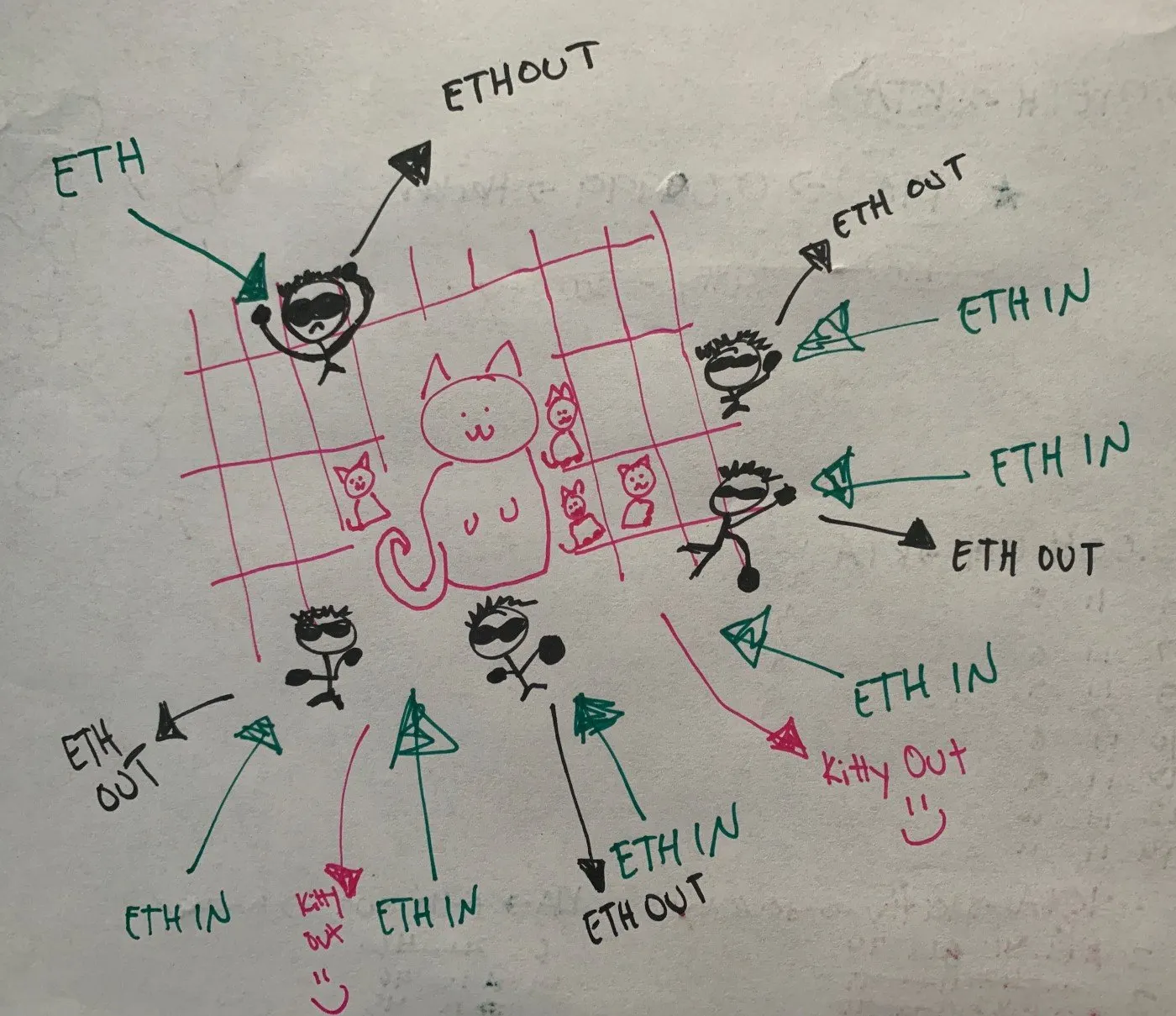
After a malicious bot connected itself to the wallet, it similarly started to reroute all incoming ETH, effectively turning the heist into a hostage situation—as there was no conventional way to free the tokens due to the lack of funds needed to pay for gas. Although, in the end the owners managed to free their poor kitties.
While some could blame such situations exclusively on the lack of personal cybersecurity wits, individual users are far from the only ones who make such mistakes. As Decrypt reported on May 19, a group of white hat hackers has recently discovered that two crypto exchanges had accidentally exposed thousands of users’ private keys, holding over $18 million in total.
Time to start looking after those private keys.