Fancycat, an international organization of cybercriminals responsible for over $500 million worth of ransomware crime, was infiltrated this summer by international law enforcement agencies working with Binance, the world’s leading exchange.
Cyber police units from Ukraine, Korea, the U.S., Spain, Switzerland, and others working with Interpol, swooped in on 21 addresses in Kyiv last June. Six members of the cybercriminal ring were accused of using malicious software, known as ransomware, in conjunction with other cybercrimes between 2019 and 2021. Their targets were the servers of Korean companies and American universities.
In a blog post detailing its involvement with the operation, Binance said, “our ongoing partnerships with law enforcement, as well as security and blockchain analytics firms, will be a driving force in improving the cybersecurity measures across the wider crypto industry.” With this in mind, over the past year, the exchange has ramped up its in-house anti-money laundering (AML) detection and analytics capabilities.
The lethal consequences of ransomware
Research demonstrates that illicit activity accounts for less than 1% of all cryptocurrency transactions, but it’s still commonly used for ransomware, which is now the biggest threat to any organization’s online security. What's more, one of the most active ransomware organizations, Clop (aka Cl0p,) has been ramping up activity in 2021, according to cybercrime researchers.
Ransomware has been used to expose healthcare records, disrupt supply chains and can have lethal consequences. Last year, in Germany, a woman died when her ambulance was turned away by the nearest hospital—ransomware had paralyzed the digital infrastructure it used to coordinate emergency treatment.
In order to launder their gains, cybercriminals often turn to cryptocurrency exchanges, and virtual asset service providers (VASPs), casting a cloud over the whole industry, according to Binance.
Platforms, which Binance dubs "Bulletproof Exchangers,” often serve as the cash-out points for cryptocurrency operations connected to financial crimes and other fraud. Typically, they have lenient know-your-customer (KYC) and AML rules.
According to Binance, “blockchain analysis shows a network of money launderers living inside macro exchanges which deposit and withdraw to each other to wash the money.”
Binance data analyzed by blockchain analytics startup TRM Labs has indicated that these platforms, often based in regions with a lack of enforcement or regulation, are linked to ransomware attacks, exchange hacks, and darknet-related activities.
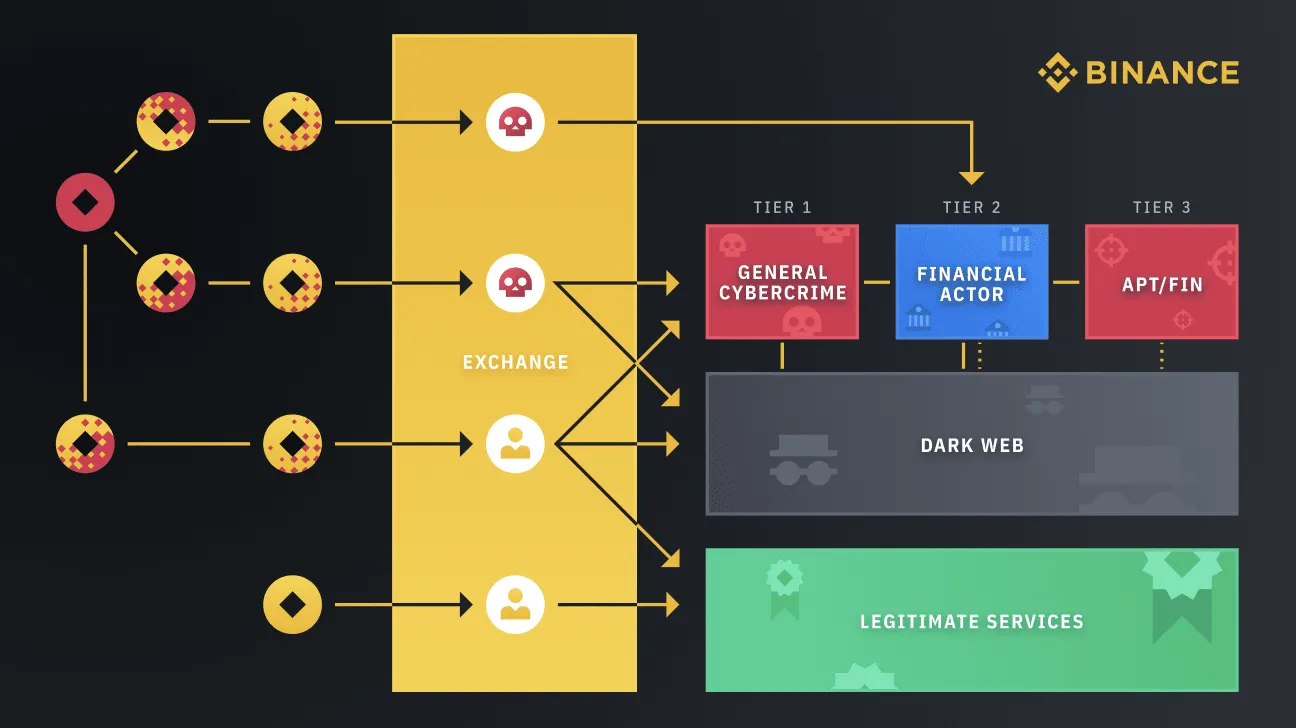
“The biggest security problem in the industry today is money connected to cyberattacks being laundered through nested services and parasite exchanger accounts that live inside macro VASPs, including exchanges like Binance.com,” says the exchange.
Continued collaboration
The Fancycat operation was not Binance’s first collaboration with international law enforcement. It set up its Bulletproof Exchanger Project in 2020; it’s a dedicated anti-ransomware initiative that saw Binance collaborate with the Ukrainian Cyber Police.
Last year, the operation identified a major cybercriminal group accused of laundering over $42 million in illicit funds.
But as well as continuing to collaborate with the authorities, the exchange is also focused on ramping up its own detection mechanisms, working with TRM, and analytics firm Crystal, developed by blockchain technology firm Bitfury.
To counter the ransomware threat, Binance has introduced mechanisms to help identify and shut down illicit activity. These are built and run by the Binance Sentry team and its analytics arm, the Security Data Science team, which identifies transactions between Binance and high-risk entities.
For example, prior to the Fancycat sting, Binance and its analytical collaborators were able to analyze on-chain activity and gain a better understanding of the group and its links to the wider criminal underworld.
Using data sets and detection algorithms trained on historical attacker data to flag potentially malicious activities, they mapped the suspect network and established that the group was linked with Clop, as well as other ransomware operations such as Petya. The analysis was key to identifying Fancycat, and led to the arrest of its members, according to Binance.
Tracking web criminals can be a lucrative business. The U.S. State Department is offering dark web informants cryptocurrency bounties in exchange for information on hackers seen as threats to the country. Around $10 million has been pledged for the enterprise.
Binance security teams are now working to apply big data techniques to further security research and investigations of crypto-related criminal activity, according to the exchange.
Via partnerships with security and blockchain analytics firms, the exchange said that it is intent on “the dissolution of additional criminal groups for an overall safer community.”
Brought to you by Binance
Learn More about partnering with Decrypt.

